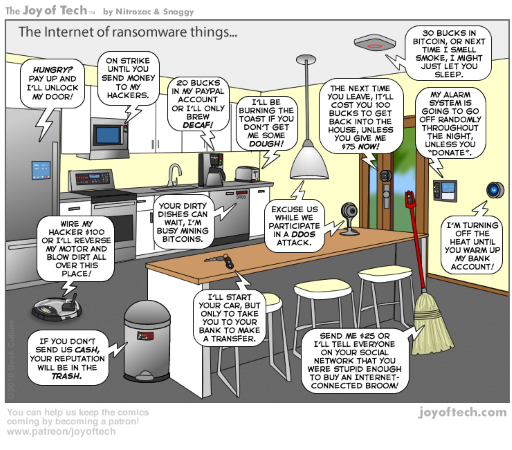
Few events on the internetz recently that caught my attention: A massive DDoS attack on the internet against a journalist Brian Krebs (https://krebsonsecurity.com/2016/09/krebsonsecurity-hit-with-record-ddos/) using insecure #IoT devices and a serious vulnerability in a medical insulin pump. (http://www.reuters.com/article/us-johnson-johnson-cyber-insulin-pumps-e-idUSKCN12411L ) Let’s start with the insulin pump.
It’s one thing to have your #IoT toaster, dvr, smart candle, fridge, etc., appliance with stupid, unnecessary internet access compromised. But when it comes to #healthcare devices, ah well, it’s plain dangerous to peoples health. #IoT future is getting scarier each day.
Firstly it must be said that the device in question here is not connected to the internet. Quote from the original rapid7 disclosure of this vulnerability
“Attack range The OneTouch Ping does not communicate on 802.11 WiFi, or otherwise communicate on the internet. However, it is believed these attacks could be performed from one to two kilometers away, if not substantially further, using sufficient elevation and off-the-shelf radio transmission gear available to ham radio hobbyists.”
Internet or no internet, nevertheless, potentially a very dangerous scenario.
Johnson & Johnson (The manufacturer of the insulin pump) stated on the Reuters article that:
“The probability of unauthorized access to the OneTouch Ping system is extremely low,” the company said in letters sent on Monday to doctors and about 114,000 patients who use the device in the United States and Canada.”
Extremely low? Well eh, that is still too much when taking in to consideration that a random hacker might kill you. This is not the first healthcare device scare where hackers can compromise the device and potentially cause such damage that the patient is killed. And I predict there will be a lot more to come.
On to the second matter, the massive DDoS (Distributed Denial of Service) attack against a journalist who is a security blogger and the French hosting provider OVH.
A botnet, Mirai was used in this attack, consisting of roughly 1.5million unprotected IoT devices, mostly internet-connected security cameras. The Mirai itself is not that sophisticated, it simply exploits the default credentials what manufactures use in their devices and take over the device. Most people, who purchase e.g. a security camera or any other internet connected IoT device do not change the default passwords on these devices. So it makes exploiting them very very easy.
The traffic that was thrown at the security blogger Brian Krebs was a huge approximately 665 Gigabits per second. OVH reported it got hit with even more junk traffic, over 1 Terabytes per second. Those numbers are so high that even the most advanced protection systems are bound to be crippled and the costs go sky high, so high in matter of fact that the company (Akamai) who was providing the protection to Brian Krebs had to take the site offline to avoid collateral damage to it’s other customers.
The attack on Brian Krebs, a journalist was a retaliation on some of his blog posts. In effect, the attackers censored his writings by taking his site down.
These massive attacks are coming more and more popular. With so many internet connected devices which are not protected we will see huge crippling attacks in the future. And I believe 1 Terabytes of traffic per second is just the beginning.
Manufactures of these IoT devices need to start taking security seriously. Stop using default credentials on their devices and either start enforcing password change at first login or use random passwords labeled on the device itself. Some even suggest Government oversight of these manufactures, forcing them to take steps to improve their devices security. Not a bad idea in my opinion.
What comes to #healthcare and #IoT, well… Stop that shit and do not make them available through a wireless connection. No no no, do not do that. It might be convenient for the user but.. ah well there’s the risk that your pacemaker will end up with that IoT toaster with default credentials.
Some very good reading below regarding and the issues I wrote about.
Insulin Pump vulnerability:
Reuters article on the Insulin Pump vulnerability: http://www.reuters.com/article/us-johnson-johnson-cyber-insulin-pumps-e-idUSKCN12411L (J&J warns diabetic patients: Insulin pump vulnerable to hacking)
The original Rapid7 blog post about the vulnerability: https://community.rapid7.com/community/infosec/blog/2016/10/04/r7-2016-07-multiple-vulnerabilities-in-animas-onetouch-ping-insulin-pump
Recent massive DDoS attacks:
KrebsOnSecurity Hit With Record DDoS: https://krebsonsecurity.com/2016/09/krebsonsecurity-hit-with-record-ddos/
The Democratization of Censorship: https://krebsonsecurity.com/2016/09/the-democratization-of-censorship/
How 1.5 million connected cameras were hijacked to make an unprecedented botnet: https://motherboard.vice.com/read/15-million-connected-cameras-ddos-botnet-brian-krebs
The Internet of Things Sucks So Bad Even ‘Amateurish’ Malware Is Enough: https://motherboard.vice.com/read/internet-of-things-malware-mirai-ddos
Future of IoT security
We Need to Save the Internet from the Internet of Things: https://motherboard.vice.com/read/we-need-to-save-the-internet-from-the-internet-of-things